Category: Microsoft Certification Exam
-
Identifying and valuing information assets-Describe security, compliance, privacy, and trust in Microsoft 365
Read More: Identifying and valuing information assets-Describe security, compliance, privacy, and trust in Microsoft 365Companies often generate vast amounts of data with varying levels of sensitivity. It is usually not practical for an organization to implement the ultimate level of security over its data, so it is necessary to classify the information according to its function and value. Therefore, the risk management process should begin with an inventory of…
-

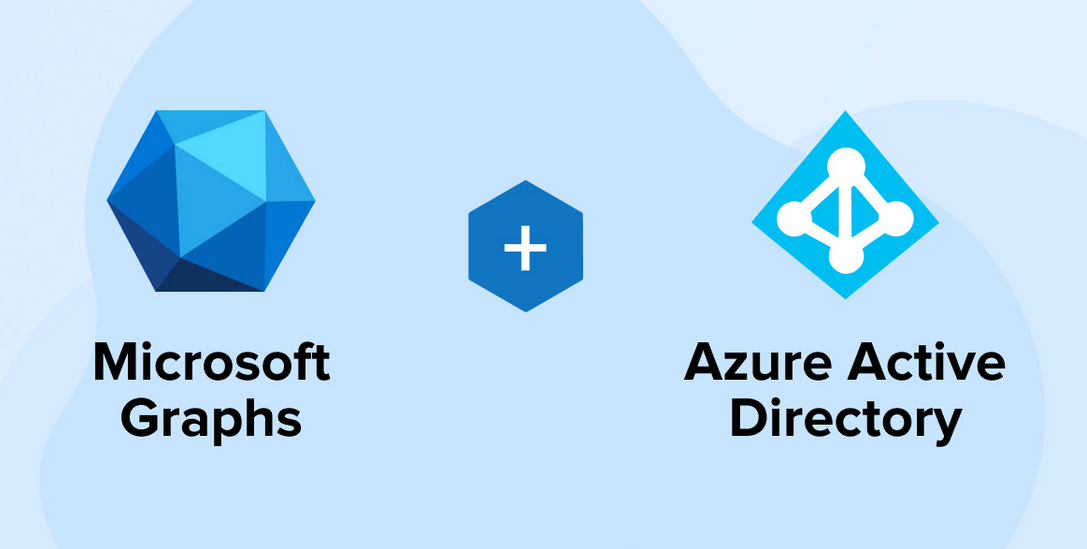
Microsoft Entra ID (Azure Active Directory Premium)-Describe security, compliance, privacy, and trust in Microsoft 365
Read More: Microsoft Entra ID (Azure Active Directory Premium)-Describe security, compliance, privacy, and trust in Microsoft 365Active Directory (AD) is a directory service that has been a part of the Windows Server product since the Windows 2000 Server release. A directory service is a database of objects, including users and computers, that provides authentication and authorization services for network resources. Authentication and authorization are essentially the front gates of information protection,…
-
Describe Microsoft Granular Delegated Admin Privileges (GDAP) principles-Describe security, compliance, privacy, and trust in Microsoft 365
Read More: Describe Microsoft Granular Delegated Admin Privileges (GDAP) principles-Describe security, compliance, privacy, and trust in Microsoft 365One of the recurrent problems for partners and other service providers supporting Microsoft 365 customers is the allocation of access permissions that enable the partner to work on the customer’s systems and services on their behalf. A feature called delegated administration privileges (DAP) has long made that possible, but DAP grants the partner full Global…
-

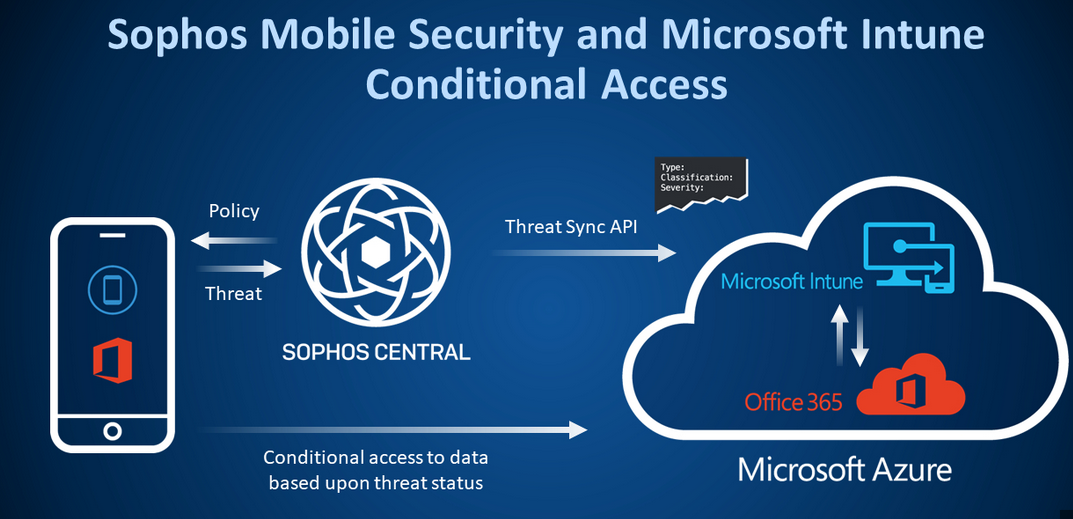
Endpoints-Describe security, compliance, privacy, and trust in Microsoft 365
Read More: Endpoints-Describe security, compliance, privacy, and trust in Microsoft 365An endpoint is any device that connects to the network from any location, whether the device belongs to the company, an employee, or a guest user. Zero Trust calls for security policies to be applied and enforced uniformly on endpoints of all types by tools such as Microsoft Intune, regardless of the users’ identities or…
-

Something you are-Describe security, compliance, privacy, and trust in Microsoft 365
Read More: Something you are-Describe security, compliance, privacy, and trust in Microsoft 365The something you are is usually some type of biometric scan. The Windows Hello for Business feature in Windows 10 and 11 supports multifactor authentication with biometric scans as one of the factors. It is also possible to use the Microsoft Authenticator app for mobile devices as a biometric scanner that enables users to access…
-
Microsoft Defender for Cloud Apps-Describe security, compliance, privacy, and trust in Microsoft 365
Read More: Microsoft Defender for Cloud Apps-Describe security, compliance, privacy, and trust in Microsoft 365Microsoft Defender for Cloud Apps is a cloud access security broker (CASB), essentially an intermediary between Microsoft 365 cloud users and the cloud-based Software as a Service (SaaS) apps they run. Like the other Defender products, the administrative interface for Defender for Cloud Apps has been integrated into the Microsoft 365 Defender portal. Defender for…
Search
Popular Posts
-
Anticipating threats-Describe security, compliance, privacy, and trust in Microsoft 365
Arguably, the most difficult part of the risk management planning process is trying to anticipate all the possible threats that could afflict the company’s data in the future. The three basic risk factors for the data—confidentiality, integrity, and availability—can be exploited in any number of specific ways, but the general threat categories are listed in…
-
Classifying users-Describe security, compliance, privacy, and trust in Microsoft 365
The third element of the digital estate that must be considered when creating a risk management plan is the people who actually access the data. Whether deliberately or inadvertently, users are a constant vulnerability—if not an actual threat—to the organization’s data. After quantifying the organization’s information assets and their value and inventorying the hardware used…