Author: Sophia Lisk
-

Something you are-Describe security, compliance, privacy, and trust in Microsoft 365
Read More: Something you are-Describe security, compliance, privacy, and trust in Microsoft 365The something you are is usually some type of biometric scan. The Windows Hello for Business feature in Windows 10 and 11 supports multifactor authentication with biometric scans as one of the factors. It is also possible to use the Microsoft Authenticator app for mobile devices as a biometric scanner that enables users to access…
-
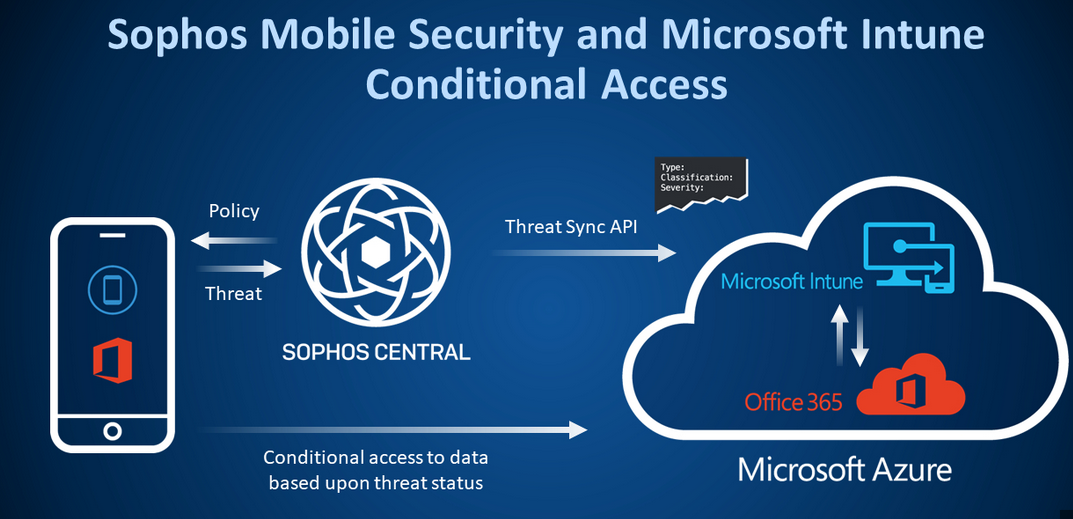
Microsoft Defender for Cloud Apps-Describe security, compliance, privacy, and trust in Microsoft 365
Read More: Microsoft Defender for Cloud Apps-Describe security, compliance, privacy, and trust in Microsoft 365Microsoft Defender for Cloud Apps is a cloud access security broker (CASB), essentially an intermediary between Microsoft 365 cloud users and the cloud-based Software as a Service (SaaS) apps they run. Like the other Defender products, the administrative interface for Defender for Cloud Apps has been integrated into the Microsoft 365 Defender portal. Defender for…
-
Describe Microsoft Secure Score benefits and capabilities-Describe security, compliance, privacy, and trust in Microsoft 365
Read More: Describe Microsoft Secure Score benefits and capabilities-Describe security, compliance, privacy, and trust in Microsoft 365Microsoft Secure Score is a feature found in the Microsoft 365 Defender portal that displays a dashboard of the network’s overall security posture, as shown in Figure 3-26. Secure Score is designed to help administrators learn more about the inner security workings of their networks. FIGURE 3-26 The Microsoft Secure Score Overview dashboard The Secure…
-

Password authentication-Describe security, compliance, privacy, and trust in Microsoft 365
Read More: Password authentication-Describe security, compliance, privacy, and trust in Microsoft 365A password is something you know, and this has been the standard means of authenticating users’ identities for many years. Password authentication costs nothing to implement, and it can be relatively secure. However, there are many possible flaws in the password authentication model. For example, passwords can be forgotten, shared, written down, easily guessed, or…
-

Protecting identities-Describe security, compliance, privacy, and trust in Microsoft 365
Read More: Protecting identities-Describe security, compliance, privacy, and trust in Microsoft 365All identities are a potential source of risk for the entire network, no matter what level of privileges they possess. Once attackers compromise one identity, it becomes relatively easy to spread laterally within the enterprise and compromise others. Therefore, administrators should try to protect all identities, not just the ones with administrative privileges. One of…
Search
Popular Posts
-
Anticipating threats-Describe security, compliance, privacy, and trust in Microsoft 365
Arguably, the most difficult part of the risk management planning process is trying to anticipate all the possible threats that could afflict the company’s data in the future. The three basic risk factors for the data—confidentiality, integrity, and availability—can be exploited in any number of specific ways, but the general threat categories are listed in…
-
Classifying users-Describe security, compliance, privacy, and trust in Microsoft 365
The third element of the digital estate that must be considered when creating a risk management plan is the people who actually access the data. Whether deliberately or inadvertently, users are a constant vulnerability—if not an actual threat—to the organization’s data. After quantifying the organization’s information assets and their value and inventorying the hardware used…